Beyond the Browser: Architecting 'ttyl' for Timeless Messages and Future Self-Connection
Imagine writing a letter to your future self. You pour your current hopes, fears, and predictions onto the page, seal it in an envelope, and tuck it away. The promise is simple: one day, a future version of you will open it and reconnect with the past.
Now, imagine doing this digitally. You type a message, maybe attach a photo or a voice note, and schedule it for delivery in 2054. This is the simple, beautiful premise behind apps like 'ttyl' (talk to you later). But beneath this simple interface lies a monumental architectural challenge.
Building an app to send a message now is a solved problem. We have WhatsApp, Slack, and Messenger. But building an app to deliver a message in thirty years? That’s an entirely different universe of engineering. The real enemy isn’t latency; it’s time itself.
How do you ensure a file saved today is even readable by the computers of tomorrow? How do you protect a message from slow, silent data corruption over decades? This isn’t just about building a chat app; it’s about architecting a digital time capsule.
The Illusion of Permanence: Why Chat Architecture Fails Over Time
When developers first search for how to build a messaging app, they find excellent guides on chat architecture. These resources are fantastic for creating real-time experiences, focusing on WebSockets, low-latency databases, and efficient message queuing.
The problem? Their entire philosophy is built for the now. They are designed for synchronous, immediate communication. An app like 'ttyl' is fundamentally different. It's an asynchronous secure application, and it requires a shift in thinking from data persistence to data preservation.
- Data Persistence: This is what standard databases do. They make sure that if you write data today, it's still there tomorrow. It's about surviving a server restart.
- Data Preservation: This is the archivist's mindset. It’s about ensuring that data written today is not just present, but also intelligible, usable, and uncorrupted decades from now. It's about surviving technological evolution.
This is the critical knowledge gap most developers face. The real challenge isn’t just storing the bits; it’s ensuring those bits still mean something in the future.
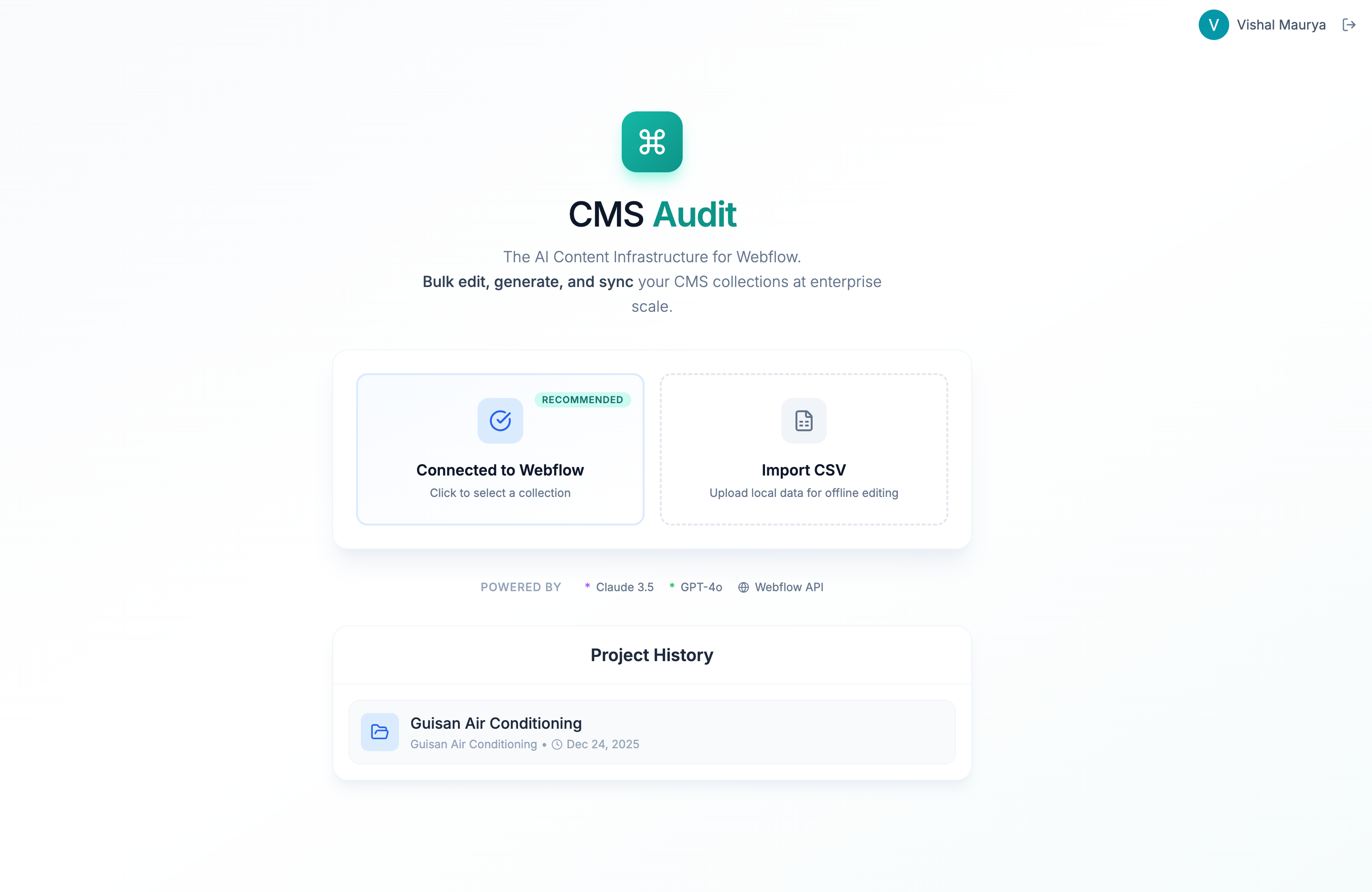
Image Placeholder: A high-level architectural diagram of 'ttyl', showing the journey of a message from creation in 2024 to delivery in 2054.
Building for Decades: The Core Architectural Pillars of 'ttyl'
To deliver on its promise, an application like 'ttyl' must be built on a foundation designed to withstand the tests of time. This involves a three-pronged approach: the ingest process, the long-term persistence layer, and the future-proof retrieval plan.
Pillar 1: The "Message Ingest" Process – Sealing the Capsule
When a user creates a message, it’s more than just saving text to a database. The application must act like a meticulous museum curator preparing an artifact for long-term storage.
- Encryption for Longevity: Standard end-to-end encryption (E2EE) is a great start, but it's not enough for the long haul. What happens if the encryption algorithm used today (like AES-256) is found to have a weakness in 2045? The ingest process must not only encrypt the data but also store metadata about the encryption itself. This includes the algorithm name, version, and the date it was applied. This creates a "Rosetta Stone" for future decryption.
- Format-Agnostic Packaging: A user might upload a
.HEICphoto from their iPhone. Will that format even exist in 2050? Instead of storing the raw file, the system should consider converting it to an open, stable format (like TIFF for images) or packaging the original file with its own specification documents. - Generating an Integrity "Fingerprint": Before being stored, a cryptographic hash (like SHA-512) of the message package is created. This unique fingerprint is stored separately. It’s the key to verifying, years later, that the data hasn't changed by even a single bit.
Pillar 2: The Persistence Layer – Defeating "Bit Rot"
"Bit rot," or silent data corruption, is a real phenomenon where stored data degrades over time without any obvious errors. For a time-capsule app, this is the ultimate nightmare. To combat this, we need to go beyond standard cloud storage and adopt principles from the world of professional data archiving.
This is where we can adapt the classic 3-2-1 backup rule for the cloud. The rule traditionally states: keep 3 copies of your data on 2 different media types, with 1 copy offsite.
For a cloud-native application, this looks like:
- 3 Copies: Store the encrypted message package in three geographically separate locations.
- 2 Providers: Use at least two different cloud providers (e.g., AWS and Azure). This protects against a provider-specific issue or a major business change.
- 1 Immutable Copy: One of these copies should be in "immutable" storage (like AWS S3 Object Lock or Azure Blob Immutable Storage), which prevents the data from being altered or deleted for a set period.
Image Placeholder: Diagram illustrating the '3-2-1 Rule for the Cloud' with AWS, Azure, and Google Cloud logos representing multi-provider redundancy.
But just storing the data isn't enough. We need an active defense system: The Data Integrity Loop. This is an automated process that runs periodically (say, once a year) and does the following for each message:
- Retrieve: Pulls one of the copies from "cold" archival storage.
- Verify: Calculates a new cryptographic hash of the retrieved data.
- Compare: Compares the new hash to the original "fingerprint" stored during the ingest process.
- Repair & Re-archive: If they match, the data is fine. If not, the corrupted copy is replaced with a healthy one from a different location. The healthy data is then re-archived, refreshing its storage lifecycle.
This active-defense loop is the single most important concept separating a true digital preservation system from a simple "save-and-pray" storage bucket.
Pillar 3: The Delivery Process – Unsealing the Future
Finally, when the delivery date arrives, the system needs to reliably retrieve, decrypt, and present the message.
This process involves reversing the ingest steps, using the stored metadata to select the correct decryption key and algorithm. It must also handle the user experience gracefully. How do you notify a user of a message sent 30 years ago? The delivery mechanism needs to be robust, likely using a combination of the user's original email, phone number, and potentially pre-designated "legacy contacts."
Image Placeholder: A visual timeline illustrating the 'Lifecycle of a Future Message', highlighting potential risks like format obsolescence and algorithm deprecation over decades.
Trust as a Feature: Privacy and the Ethics of Time
An application like 'ttyl' isn't just storing data; it's holding onto people's memories, secrets, and emotions. Trust is not a byproduct; it is the core feature. This requires absolute clarity on privacy and data handling:
- Zero-Knowledge Architecture: The service should be unable to decrypt the user's data. Only the user (or their future self) holds the key.
- Data Portability: Users should have a way to export their encrypted time capsules, ensuring they aren't locked into a single platform forever.
- A Sustainable Business Model: Users need to believe the company will still exist in 30 years. This means a transparent business model that doesn’t rely on selling the very data it's sworn to protect.
Building vibe-coded applications like 'ttyl' pushes the boundaries of what we consider possible. It forces us to think beyond immediate user engagement and architect for legacy. It's a fascinating challenge that blends secure software engineering with the principles of digital archaeology. For developers looking for inspiration for AI-assisted projects, this new frontier of long-term, asynchronous applications offers a world of meaningful problems to solve.
Frequently Asked Questions (FAQ)
What is a digital time capsule?
A digital time capsule is a collection of digital files (like documents, photos, videos, or messages) that is created and sealed to be opened at a specific future date. Unlike a physical time capsule, it relies on digital preservation techniques to ensure the data remains accessible and uncorrupted over long periods.
Isn't this just like scheduling an email?
Not at all. Scheduling an email relies on the email provider (like Google) continuing to exist and maintain your account in its current state. A true digital time capsule application is architected independently to survive technological shifts, company closures, and data degradation over decades, a far more complex technical problem.
How do you handle a user losing their password over 20 years?
This is a critical challenge. Solutions often involve a "social recovery" mechanism where a user pre-designates trusted contacts who can collectively approve an access request. Another method is a "key escrow" system where fragments of a recovery key are stored in multiple, highly secure locations, requiring a rigorous identity verification process to reassemble.
What are the biggest risks to the long-term data?
The three biggest risks are:
- Data Corruption ("Bit Rot"): The silent, gradual degradation of data stored on physical media.
- Format Obsolescence: The inability to open a file because the software that created it no longer exists (e.g., trying to open a file from a 1990s word processor).
- Company Failure: The service provider going out of business, taking all the stored data with it. This is why data portability and sustainable business models are so crucial.
Ready to see what else is possible with creative coding? Head over to Vibe Coding Inspiration to discover, remix, and draw inspiration from a curated collection of innovative projects.
.svg)