Privacy-by-Design in Mental Wellness Apps: An Ethical Guide for Developers
You’re building an AI-powered journaling app. Your "vibe-coding" approach is brilliant—it doesn't just store text; it analyzes sentiment, tracks mood shifts, and offers gentle nudges based on the user's emotional state. It’s designed to help people. But have you considered that you're building one of the most intimate data repositories imaginable?
Here’s a sobering fact that should stop every wellness app developer in their tracks: a recent study found that 29 out of 36 of the top mental health apps shared user data with third parties like Facebook and Google. This isn't just a technical misstep; it's a fundamental breach of trust at a moment of profound vulnerability for the user.
As a developer, you are the final gatekeeper of user privacy. Legal teams write policies, but you write the code that enforces them—or doesn't. This guide is for you. It’s not about legal jargon or business strategy; it's about translating the core principles of Privacy-by-Design (PbD) into the code you write, the architecture you plan, and the ethical standards you uphold every day.
What is Privacy-by-Design, and Why Is It Non-Negotiable?
Privacy-by-Design isn't a feature you add at the end of a sprint or a checkbox on a compliance form. It's a philosophy, developed by Dr. Ann Cavoukian, that mandates privacy be baked into the very foundation of any system or technology. Instead of fixing privacy breaches after they happen, you design your app so they can't happen in the first place.
For a mental wellness app, this isn't optional. Users are sharing thoughts they might not even tell their therapist. The data isn't just "personal"; it's a map of their mental state. To treat it with anything less than the utmost care is an ethical failure. By adopting PbD, you shift from simply complying with regulations to genuinely protecting your users.
The 7 Principles of Privacy-by-Design, Translated for Developers
Let's break down the seven foundational principles of PbD and translate them from abstract concepts into concrete actions you can take in your IDE.
1. Proactive not Reactive; Preventative not Remedial
This principle means you anticipate privacy risks before they materialize. You don't wait for a data breach to happen; you build safeguards to prevent it from the start.
What this means for your code:
- Threat Modeling: Before writing a single line of a new feature, map out how data will flow. Ask, "Where could this data leak? How could it be misused? Who could access it?"
- Input Validation: Sanitize all user inputs rigorously to prevent injection attacks that could expose user data.
- Dependency Audits: Regularly audit your third-party libraries. A vulnerability in a dependency is a vulnerability in your app.
| Do This | Don't Do This || :--- | :--- || Conduct a privacy threat model during the feature planning phase. | Assume your frameworks (e.g., Express, Django) handle all security by default. || Use secure coding libraries like OWASP ESAPI for validation. | Write your own complex validation or encryption functions unless you're a security expert. |
2. Privacy as the Default Setting
Users shouldn't have to navigate a maze of settings to protect themselves. The most private, secure options should be enabled by default, without any action on their part.
What this means for your code:
- Opt-in, not Opt-out: All data sharing or non-essential data collection features should be
falseby default. The user must actively choose to turn them on. - Minimal Permissions: When your app asks for permissions (location, contacts), request the narrowest scope possible and only when the feature requiring it is actively used.
- Data Minimization: Collect only the absolute minimum data required for a feature to function. If you don't need it, don't ask for it, and don't store it.
| Do This | Don't Do This || :--- | :--- || const shareAnalytics = false; // User must explicitly set to true | const shareAnalytics = true; // Hope the user finds the setting to turn it off || Make "Share My Journal with a Friend" an explicit, one-time action. | Default all new journal entries to "Public" or "Shareable". |
3. Privacy Embedded into Design
This is the heart of PbD. Privacy isn't a layer you paint on top of your app; it's part of the architectural blueprint. It influences your database schema, your API design, and your data flow.
What this means for your code:
- On-Device Processing: Whenever possible, process sensitive data directly on the user's device. For a mood-tracking app, sentiment analysis of a journal entry can happen locally, with only the anonymized result (e.g.,
{ mood: 'positive', score: 0.8 }) sent to your server. - Anonymization & Pseudonymization: Before storing data, strip it of personally identifiable information (PII). Replace
user_id: 123withpseudonym: 'xyz789'. Don't store a user's precise location; store the city or region. - Secure API Endpoints: Design your APIs to expose the minimum data necessary. An endpoint to fetch mood trends should not also return the raw journal entries associated with those moods.
Image: Diagram showing Privacy-by-Design integrated at every stage of the software development lifecycle, from ideation to deployment, contrasted with a linear model where privacy is an afterthought.
4. Full Functionality—Positive-Sum, not Zero-Sum
Privacy and user experience are not opposing forces. You don't have to sacrifice a great feature to protect privacy. The challenge—and the opportunity for innovation—is to achieve both simultaneously.
What this means for your code:
- Creative Solutions: Instead of asking for access to all contacts to find friends on the app, allow users to share a unique invite link. Instead of tracking background location, let the user manually tag a location to their journal entry if they choose.
- Focus on the Goal: A feature that "nudges" a user to go for a walk when they feel down doesn't need their precise GPS history. It only needs to know they haven't moved much that day, which can be derived from the phone's step counter API, not by tracking their every move.
| Do This | Don't Do This || :--- | :--- || Achieve the feature's goal with less invasive data. | Demand invasive permissions because it's the easiest or most obvious way to build a feature. || Offer a feature that works well without any data sharing, but is enhanced if the user opts-in. | Cripple your app's functionality until the user agrees to broad data collection. |
5. End-to-End Security—Full Lifecycle Protection
Data security isn't just about encrypting your database. It's about protecting data from the moment it's created until the moment it's securely deleted—on the device, in transit, and at rest on your servers.
What this means for your code:
- Encryption Everywhere: Use TLS for all data in transit (API calls). Encrypt data at rest in your database (e.g., AWS KMS, Azure Key Vault). For extremely sensitive data like journal entries, consider client-side encryption where the data is encrypted on the device before it's ever sent to your server.
- Secure Deletion: When a user deletes their account, you must actually delete their data. This means implementing hard deletes, not just setting an
is_active = falseflag in your database. Ensure this cascades to backups and logs in a reasonable timeframe. - Secret Management: Never hardcode API keys, database credentials, or encryption keys in your source code. Use a secure secret manager like HashiCorp Vault or AWS Secrets Manager.
6. Visibility and Transparency—Keep it Open
Your users should never be in the dark about what data you collect or how you use it. This means having a clear, human-readable privacy policy and being honest within the app's UI itself.
What this means for your code:
- Just-in-Time Explanations: When you ask for a permission, explain why you need it in plain language. Instead of a generic "Allow location access?" prompt, use: "Allow access to your city to provide localized mental health resources?"
- Accessible Data: Build a feature that allows users to easily view and export all the data you have stored about them. This isn't just good practice; it's a requirement under laws like GDPR.
7. Respect for User Privacy—Keep it User-Centric
This final principle is a summary of all the others. The user is the owner of their data. Your role is that of a custodian. Every decision you make should be in their best interest, empowering them with control and choice over their personal information.
Gut Check: Ask yourself this question: "Could I explain my app's entire data flow to a user, on a whiteboard, without feeling like I was misleading them?" If the answer is no, you have work to do.
The Vibe-Coding Challenge: Protecting Implicit Data
Many of the most powerful vibe-coded projects excel at gathering implicit data—information the user doesn't provide directly. This could be:
- Sentiment derived from a journal entry.
- Speech patterns from a voice note.
- Typing speed and pressure.
This data is incredibly sensitive and requires an even higher standard of care. The most robust architectural pattern for this is on-device processing.
Image: Architectural diagram comparing two data flows. Left side: "Traditional Approach" showing sensitive user data sent to a central server for processing. Right side: "Privacy-by-Design Approach" showing data being processed on the user's device, with only anonymized or essential results sent to the server.
By running your AI models directly on the user's phone, you can perform tasks like sentiment analysis without the raw, sensitive text ever leaving their device. You get the valuable insight needed for your feature, and the user gets absolute privacy.
Your Privacy-by-Design Questions, Answered
Is this just another term for GDPR or HIPAA compliance?
No. Regulations like GDPR and HIPAA are legal frameworks that set a minimum bar for compliance. Privacy-by-Design is an ethical and engineering philosophy that aims for the highest standard of user protection. If you correctly implement PbD, you will likely meet and exceed the requirements of these laws, but compliance is a result of good design, not the sole objective.
This sounds like it will slow down development. Will it?
Initially, it requires more thought during the design phase. However, building privacy in from the start is far cheaper and faster than trying to bolt it on later. A data breach can destroy your company overnight. A privacy scandal can erase user trust forever. Fixing privacy flaws in a mature codebase is complex and expensive. PbD is an investment that pays for itself.
Where do I even start with my existing app?
Start with an audit. Map your app's data flows and identify the most sensitive data points. Begin with the principle of "Privacy as the Default." Go through your codebase and change all non-essential data collection to be opt-in. Then, focus on data minimization. Are you storing data you don't actually need? Delete it. Small, incremental steps are better than no steps at all.
Your Next Step: Become an Ethical Architect
Building AI-assisted applications for mental wellness is a profound responsibility. You have the power to create tools that genuinely help people navigate complex emotional landscapes. You also have the power to do immense harm if you are careless with their trust.
By embracing Privacy-by-Design, you are not just writing better code; you are making an ethical commitment to your users. You are choosing to build products that respect them, protect them, and empower them.
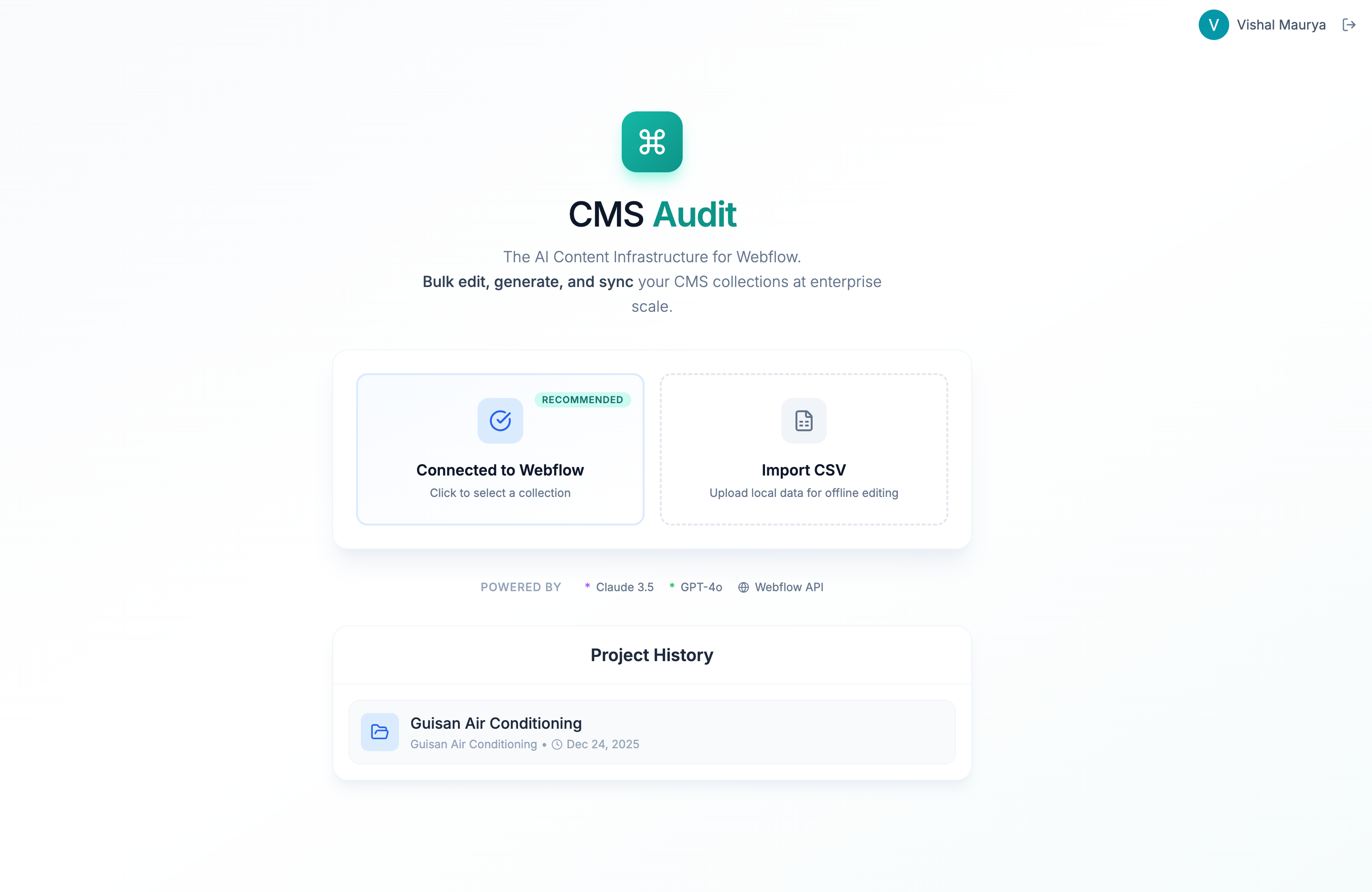
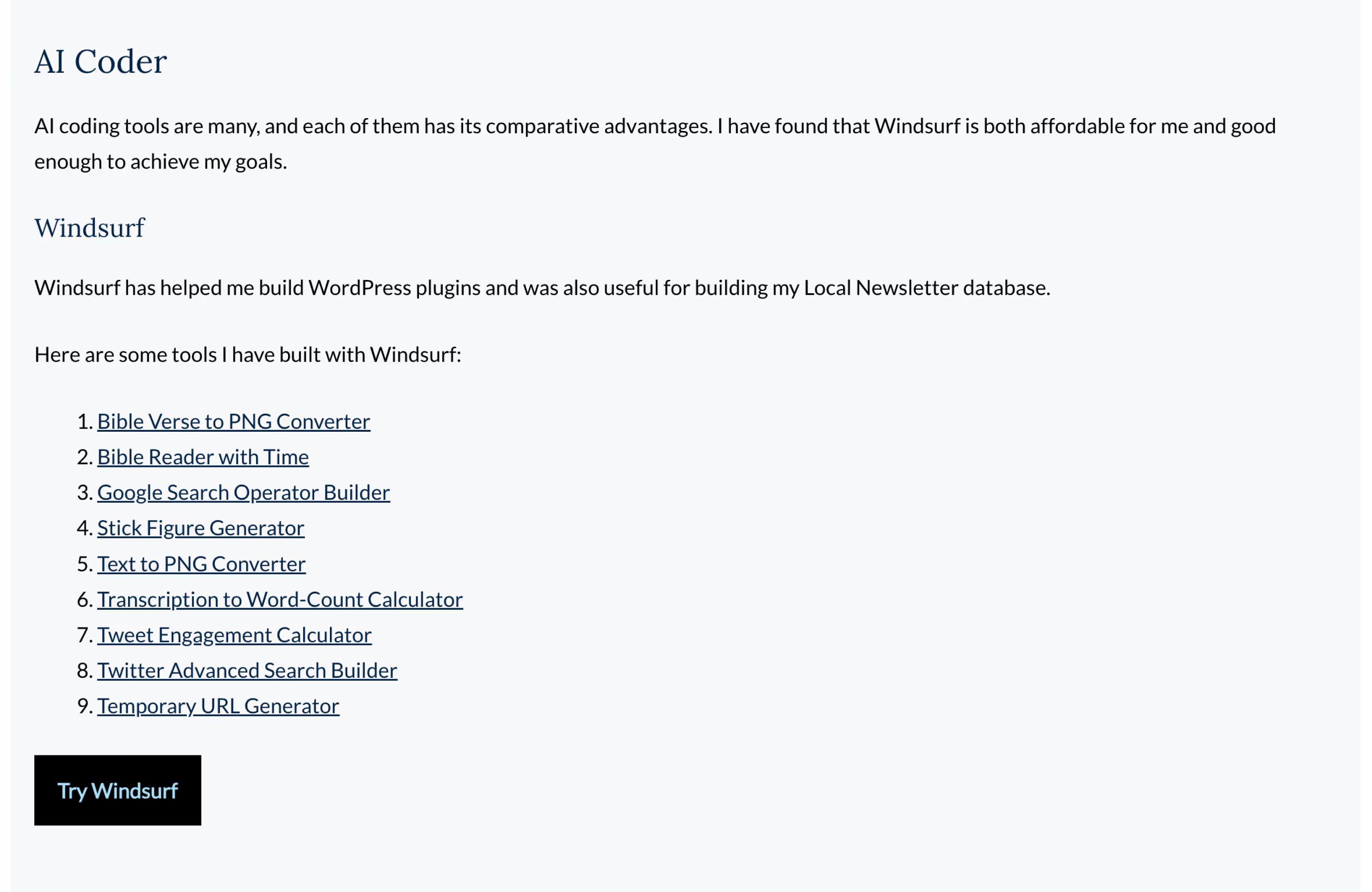
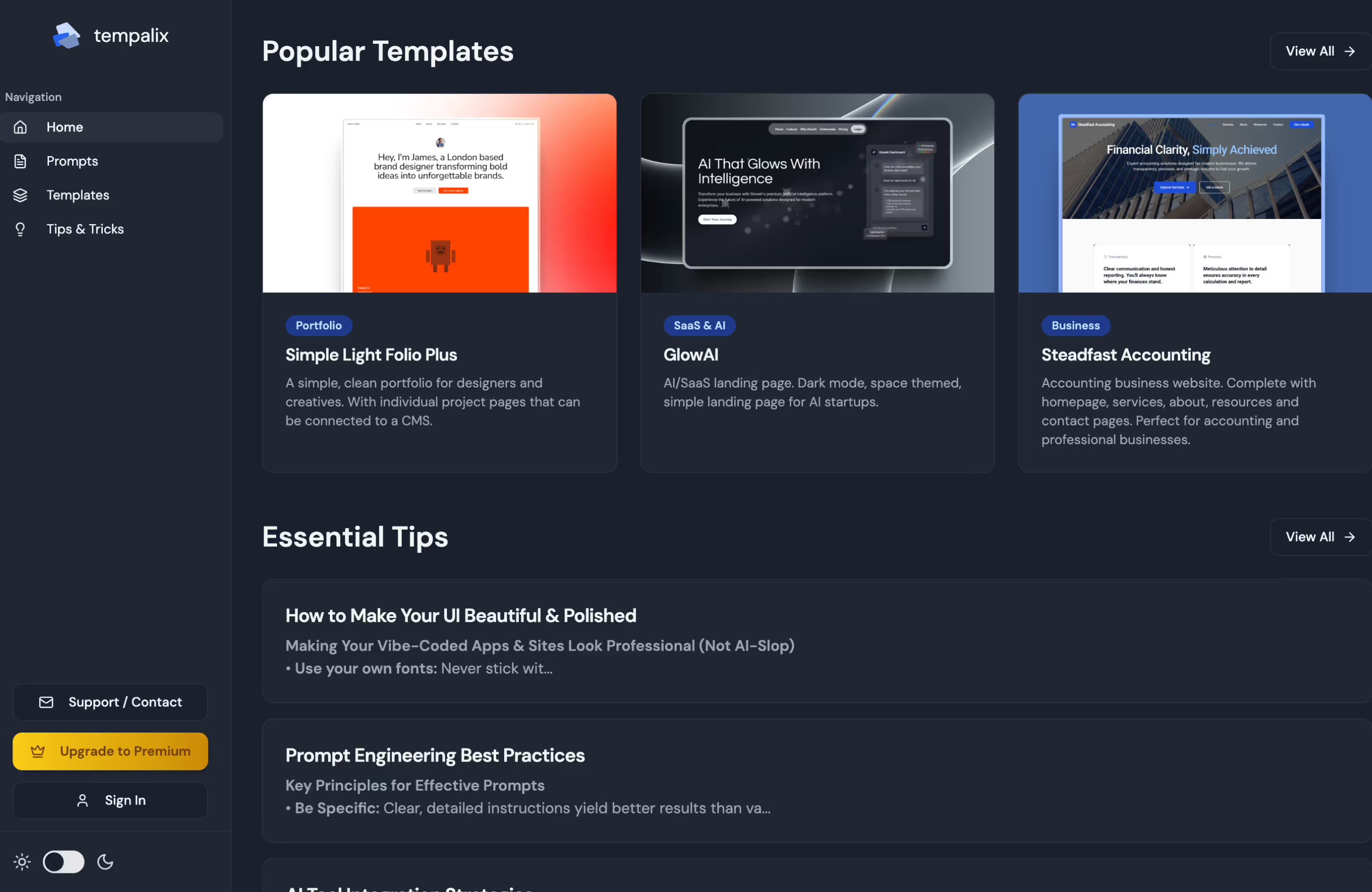
For more examples of how developers are building innovative and user-respecting tools, browse the collection of projects on Vibe Coding Inspiration. See what’s possible when great technology is guided by a strong ethical compass.
.svg)